Private EMS Agencies
Cybersecurity for Private Ambulance Services
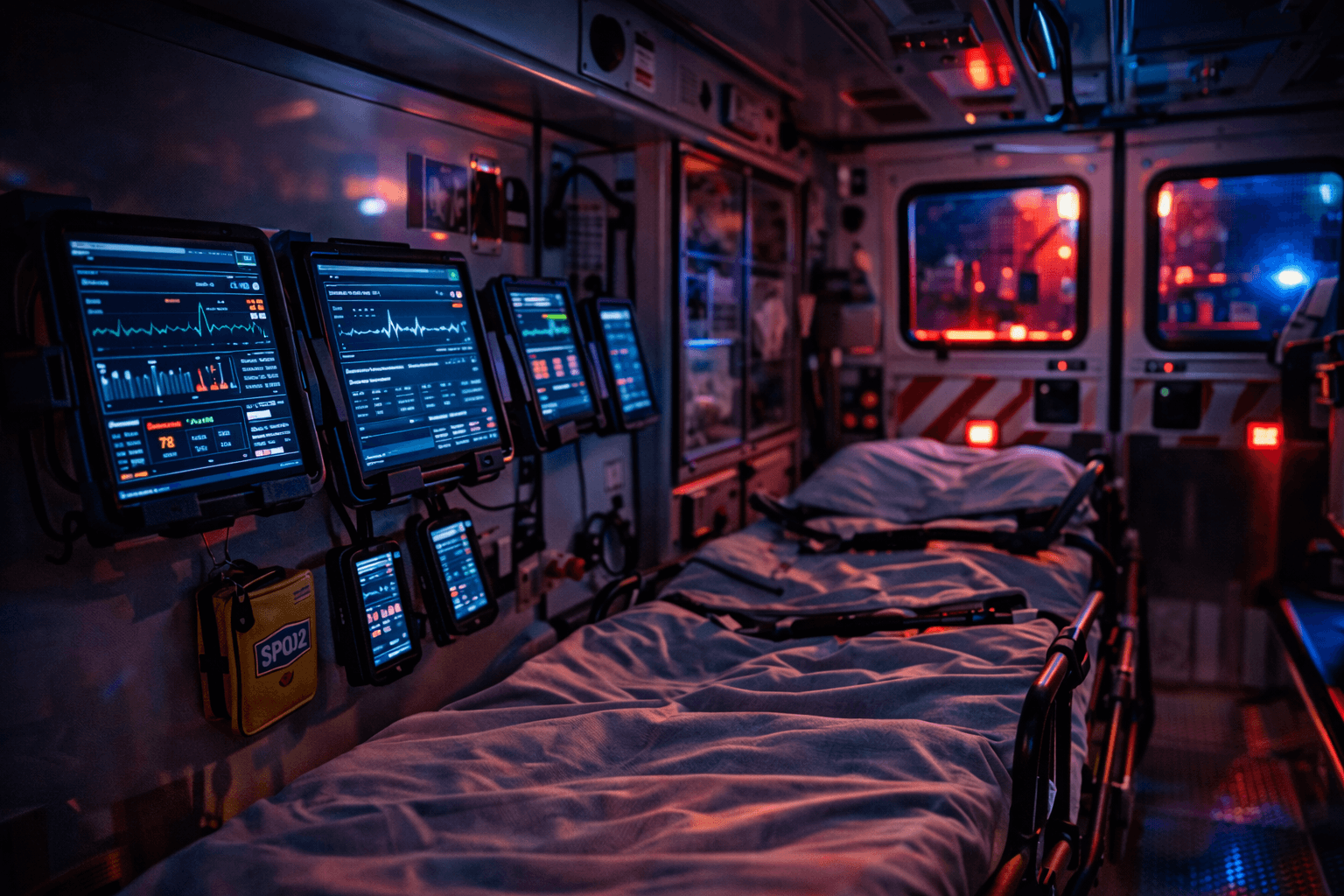
Private EMS operations handle sensitive patient data across vehicles, crews, facilities, and jurisdictions every day. That creates a very different cyber risk picture from a hospital campus or a generic office environment.
Iron Rod Security helps private ambulance services understand what happens when ePCR, CAD, billing, connectivity, or fleet devices fail, and what to prioritize before those failures turn into a patient-care or revenue crisis.
What tends to break first in private EMS
In many private EMS environments, the first visible problem is not a formal data-breach notice. It is an operational failure: crews lose access to ePCR, dispatch data stops flowing, billing queues freeze, or a fleet of field devices becomes unreliable during transport. That is why advisory work has to map technology to operations, not just controls to compliance language.
Risks specific to private EMS
ePCR data exposure
Patient care reports contain PHI transmitted wirelessly from the field. A compromised device or unsecured network exposes the agency to HIPAA violations and breach risk.
CAD system downtime
Dispatch and routing systems are operational infrastructure. Ransomware or vendor outage means crews cannot receive assignments, coordinate responses, or track locations normally.
Fleet device sprawl
Tablets, phones, MDTs, and hotspots are distributed across vehicles and crews. Each device can access patient data and each one is a potential entry point.
Third-party vendor risk
ePCR, billing, scheduling, and fleet tools all create dependency risk. A breach or outage at one vendor can still become your incident.
Billing system compromise
Billing platforms hold patient demographics, insurance data, and financial records. A compromise affects both revenue continuity and sensitive-data exposure.
How we help private EMS agencies
Common questions from private EMS agencies
What makes private EMS cybersecurity different from hospital cybersecurity?
Private EMS depends on moving crews, mobile devices, vehicle connectivity, dispatch coordination, and vendor-managed systems that do not behave like fixed clinical environments. The operational risk sits in transit, handoff, and uptime rather than in a single facility network.
If our ePCR vendor is secure, aren't we covered?
No. Vendor security matters, but the agency still owns field-device hygiene, account control, wireless risk, workflow gaps, and the continuity plan for what happens when the platform or integration is unavailable.
Do smaller IFT companies face real cyber risk?
Yes. Attackers do not need a large fleet to profit from stolen PHI, ransomware, or credential abuse. Smaller operators are often easier to disrupt because they have fewer fallback processes and less dedicated security oversight.